Fingerprint Employee Clocking System
Debrah Joshua Osei*, Mohammed Issah Adinkrah, Lord Anertei Tetteh, Abigail Mba and Kojo Boakye
The University of Energy and Natural Resources, Sunyani, Ghana
Submission: October 30, 2020;Published: December 10, 2020
*Corresponding author: Debrah Joshua Osei, The University of Energy and Natural Resources, Sunyani, Ghana
How to cite this article: Debrah J O, Mohammed I A, Lord A T, Abigail M, Kojo B. Fingerprint Employee Clocking System. Trends Tech Sci Res. 2020; 4(4): 555645. DOI:10.19080/TTSR.2020.04.555645
Abstract
A system that is used for time-clocking, creating an all-inclusive electronic record of the process involved in how employees logs in and out of work on working days are referred to as a clocking system. The system has an additional feature of calculating an accurate payroll system, which in turn, can lead to a precise amount the company spent on labour. In essence, an employee clocking system is a process of monitoring the attendance, presence and truancy of employees in a work environment. In this project, the University of Energy and Natural Resources was used as a case study. The existing method of recording the presence of staff to work is by a manual process where employees record their attendance on a paper. The challenge of the existing employee attendance system is the difficulty in tracing old records, safekeeping, lack of confidentiality and the chances of other employees logging in for their truant colleagues. This paper sought to introduce a biometric employee clocking system to help overcome the high level of truancy in workplaces. The results of the experiment we conducted indicate a high accuracy in our system with TAR value of 99.7%. This accuracy rate is much better than the results other researchers obtained. The good accuracy implies that employees will have difficulty to check-in or out for their truant colleagues. The high accuracy results will help improved security of attendance, improved employee performance, ensures fast and easy retrieval of data, easy monitoring of staff, and prevent impersonation in the attendance logs.
Keywords: Control mechanisms; Digitization; Biometric systems; Fingerprint scanner
Introduction
Employee Clocking System (ECS) is an electronic process of monitoring the attendance in the work environment to minimize economic, time, productivity and loss revenue due to employee absenteeism, lateness and truancy. Attendance monitoring and evaluation have traditionally been approached using time clocks and timesheets (the manual way of taking employee attendance). However, attendance monitoring and evaluation goes beyond only attendance, but it ensures efficient time utilization which maximizes and motivates employee attendance. Employee Clocking System is the easiest way to keep track of employees’ attendance and productivity in industrial organization, business organizations and volunteer groups. Employee Clocking System is useful in terms of workforce analysis, day-to-day monitoring of attendance, maintaining statutory registers, leave records, calculation of overtime and transferring information to the payroll system [1].
The existing employees’ attendance system requires the employees to manually log the attendance sheet every time they come to the office, and when they close [2]. Typically, such a system lacks automation because it is not an electronic system and might generate a number of problems. These problems may include the time unnecessarily consumed by the workers to find and sign their name on the attendance sheet and the fact that the attendance sheet may get misplaced or kept away from employees due to suspected wrong activities. The development and implementation of this system will help organizations to manage their employees’ attendance systematically. The system has a database that contains employee’s information, and it will help the admin to manipulate data and update the database [2,3].
In today’s business transactions, it is always expected that the clients authenticate themselves for services rendered to them with control mechanisms such as identity card, ATM card, driving license, health card and so on. Carrying different cards and remembering passwords for different services is a complex issue for individuals and organizations [4]. Secure and effective identity and access control system plays a vital role in the successful deployment of an Employee Clocking System. To make the identification and access control mechanism safe and reliable for authentication, the Employee Clocking Systems must have integrated biometric data as an added feature. The move towards the digital era is being accelerated every hour globally to meet the evolving digitization and smart system development. Biometrics technologies verify identity through characteristics such as fingerprints, faces, iris, retinal patterns, palm prints, voice, and hand-written signatures and so on. This biometric authentication present fingerprint as the most common and popular biometric used in automatic personal identification [5,6].
Literature Review
Theories, as well as models, provide a basis that guides research and interpretation of research results [7]. In research, theories are formulated to assist in explaining, predicting, and understanding phenomena. In biometric systems, according to [8,9], staff attendance is taken electronically with the help of a Biometric fingerprint system, and all the records saved for subsequent operations. [10,11] argued vehemently that, biometric systems are an authentication method. As suggested in [7,12,13], biometric systems identify people by recognizing one or several physical characteristics. It is one of the future main solutions for providing authentication. Fingerprints are considered to be the best and fastest method for biometric identification because they are secure to use, unique for every person and do not change in one’s lifetime [11,12]. Therefore, this study is concerned with the implementation of a biometric fingerprint authentication system which is an automated method of verifying a match between two human fingerprints for validating identity.
Employee clocking system using fingerprint biometric identification technique employs an automated system to calculate staff attendance and do further calculations of daily and monthly attendance summary in order to reduce human errors during calculations. In essence, our system can be employed in curbing the problems of ghost names (people whose names are on the payroll and receiving pay yet are not delivering any services to the institution), the lateness of workers to their various posts, impersonation and missing working periods in any institution. The system will also improve the productivity of any institution if properly implemented.
Biometric Resource-Based Theory
The study was anchored in the Resource-Based Theory (RBT). There is evidence from research that supports the RBT [14] that argues that organizations compete in a dynamic and changing business environment. Firms can attain and achieve a sustainable competitive advantage through their employees, according to [12]. This can be realized when organizations have a pool of human resources that cannot be imitated or substituted by their rivals or competitors.
The RBT as a foundation of competitive advantage is embedded in the utilization of a bundle of valuable resources that are at the disposal of the firm. It is important that firms have to identify the major potential resources. These resources should be valuable, rare inimitable and non-substitutable among the competitors of the firm [11] in the field that they operate in. Firms’ resources must be valuable in order to make firms adopt valuecreating strategies. The firm should outperform its competitors or minimize the weaknesses that it may have [12]. The RBT as a foundation for the competitive advantage of firms’ is embedded mainly in the use of tangible or intangible resources that firms may have [3,15]. The RBT looks at the firm’s internal operational environment as an important driver that can create a competitive advantage for the firm.
The RBT assumes that an organization is made up of unique capabilities and resources as a foundation for a firm’s strategy to compete and be profitable and also have a competitive advantage over its competitors. According to Hitt, Ireland and [10], firms can use the resources at their disposal and capabilities to enhance their operational performance. In order to be competitive, firms should ensure that they carry out their activities in an integrated approach. Firms should also adopt strategies that distinguish them from other firms in the areas that they operate in. As a result, organizations need to explore their frameworks if they envisage remaining relevant in the context of the competitive global environment. Organizations are striving to achieve a competitive advantage, and they should put into consideration that true competitive advantage requires the resources of an organization to be valuable, rare, inimitable and non-substitutable as pointed out by [5,9].
The key aspect of the Resource-Based Theory is that firms have to identify their main resources that can make the firms to achieve and sustain a competitive advantage against their competitors [11]. A resource has to be valuable to organizations like UENR, Sunyani is expected to make optimum use of time and the human resources that they have by ensuring that employees work fully for the scheduled time to enable UENR to enhance its operational performance in the delivery of administrative services.
Computerized Biometric Employee Clocking System and Operational Performance
When computerized biometric employee clocking systems are being designed, it is important to ensure that physiological and behavioural features are taken into consideration [16]. The ultimate performance of the biometric system will depend on how well the physiological and behavioural features were considered in the biometric system design. The features that need to be considered include the uniqueness of individual users, permanence, acceptance, and hardness of the system and levels of fulfilment [13]. Biometrics systems help in effective attendance management which helps in increasing employee or workers’ productivity and generate time and overhead cost savings to enhance the organizations’ performance by utilizing computerized time management system to track employee time and attendance [8,13]. Attendance timing management helps in guiding our methods of managing working hours. The actions that are taken to enhance efficiency was based on the principle of time management [7].
Fingerprint Level 1 and Level 2 Features Enhancement to Improve Quality of Image
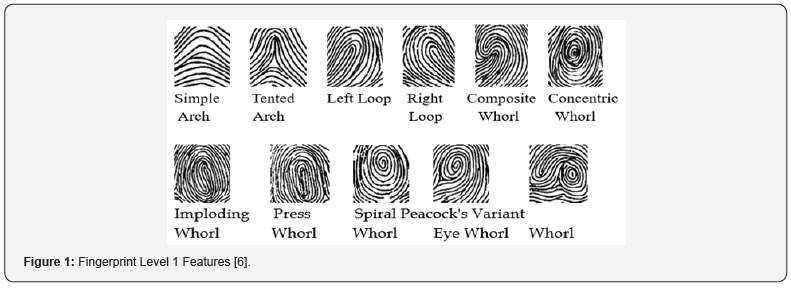
Fingerprint recognition is one of the exciting and complex image processing problems, which requires a constant and continuous contribution to new research from the research community. Even though the face recognition is automatic pattern recognition system and controlled by the computer, the performance of the system is directly dependent on the quality of the fingerprint images and the quality of the image capturing device [15]. Level 1 feature comprises of the orientation of the fingerprint, core-centre from which ridge ending and ridge pattern named and delta location-point on the friction ridge and distinction of finger versus palm. As shown in Figure 1, Level 1 Features’ examples include Simple Arch, Tented Arch, Right Loop, Left Loop, Composite Whorl, Concentric Whorl, Imploding Whorl, Press Whorl, Spiral Whorl, Peacock’s- Eye Whorl and Variant Whorl [17]. Loop pattern Ridges enters from either side of the impression or pattern, re-curves or touches an imaginary line drawn from delta to the core and terminates on the same side from where it is originated. In Arch, pattern ridges start from one side of the fingerprint pattern to another side without doing backwards turn. Whorl pattern consists of series of circles which starts from an arbitrary point and ends at the same point [7,11,12], with only Level 1 features, fingerprint recognition systems neither recognize the image nor identify or verify the image [10]. Level 1 feature is mainly used for classification, verification, filtering, and enhancement purpose.
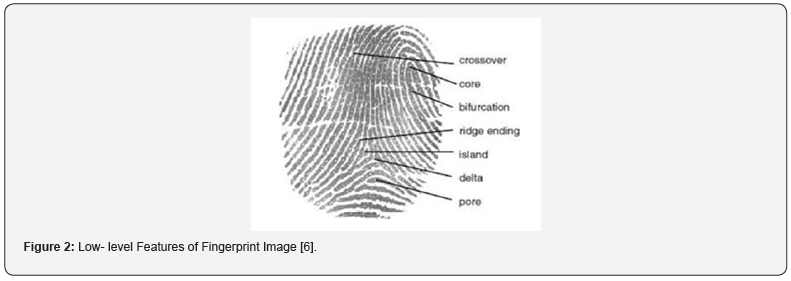
The primary purpose of Level 1 features- ridge pattern or flow and orientation in Figure 1 above, are mainly used for image enhancement and orientation purpose, which will improve the quality of fingerprints. If the image contains noisy regions, it is difficult to define the orientation of the image. Image enhancement techniques are essential or necessary because the image captured through a sensor or optical device is not assured quality [5,18]. Fingerprint image enhancement is technically done by improving the quality of ride pattern or increasing the consistency of ridge orientation, which means level 1 feature, is exposed and analyzed. Ridge ending and ridge bifurcation or minutiae points are level 2 features. Still, some other features like line unit, line fragment, eye, and hook also can be extracted and studied, which are referred to as low-level fingerprint features [19]. The low-level features are shown in Figure 2.
Methodology
The research was localized at the UENR campus, as a case study. A web application was designed and installed on three computers. Each computer had a fingerprint scanner device attached to the computer to receive or reject fingerprints images. In this study, 1000 participants (population) were selected for the fingerprint experiment. The participants included students, teaching and non-teaching staff. The design phase of the employee clocking system integrated the biometric fingerprint scanner to a web application [20,21]. The web application is a common platform for all the fingerprint devices which connect to a single database [22,23]. It involved dividing the whole system into modules and defining the relationship among the constituent modules. The topdown design approach was employed, which involved dividing the system into subsystems or modules, and each subsystem is further divided into even smaller subs. This process of division is repeated until each module is sufficiently small enough to be conveniently coded as an independent entity that performs a clearly defined operation.
The population of the study
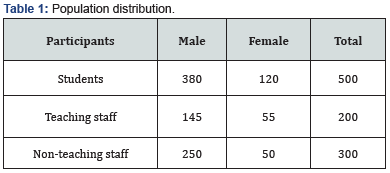
A total population of 1,000 employees and students at UENR were selected randomly to participate in the biometric fingerprint experiment. The distribution of the population has been represented in Table 1.
Sampling Procedure and Sample Size
The sampling process has been divided into two phases. The first phase randomly selected 500 students. The system is envisaged to be used in the classroom to monitor students’ class attendance. The second phase was a careful selection of teaching and non-teaching staff. In all these phases, the availability of the participants for the experiment was taken into consideration. Table 1 represents the sample size for the research. The sample size has been calculated through Slovin’s formula [17] by using a confidence level of 85%.

In the Slovin’s formula, N is the total population, e is the error of tolerance, and n is the sample size. The total population consists of 7,200 participants selected from the University. With the help of Slovin’s formula, 1,000 sample size has been calculated to conform to the population segmentation with a response rate of 98%.
Research Design and Analysis
The study has been designed to improve employee attendance at the universities and other related organizations. The employee clocking system comprises of a database, web application [20] and the finger. The fingerprint’s Software Development Kit (SDK) we used to design the web application, and the database [22] includes JavaScript, PHP, MySQL and C#. The analysis of the result was done by using SPSS software and M.S. Excel and visual studio. Values from the tables generated by the SPSS were also tested in Excel using formulas. The system [24,25] consists of the attendance software installed on an HP 630 Laptop with 64-bit Operating System (Windows 10), 1 Terabyte Hard disk, 16 Gigabytes RAM and 4 Gigahertz (Intel Pentium Processor) and a fingerprint scanner. The developed application was installed on three computers and the fingerprint scanner as well, to communicate with the application software. The computer has been labelled System 1, System 2 and System 3. The developed system was tested, and every bug detected was corrected for system worked perfectly.
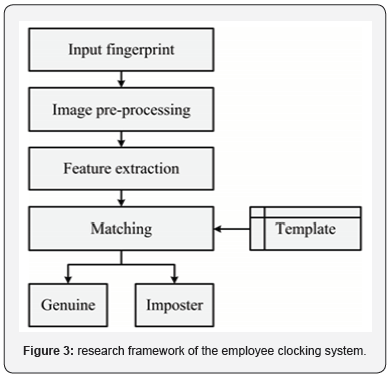
Flowchart of the Employee Clocking System
The flowchart presented in Figure 3 shows the visual representation of the sequence of steps and decisions needed to perform a process involved in the ECS. Each step in the sequence is noted within a diagram shape. Connecting lines and directional arrows link steps. This allows readers to view the flowchart and logically follow the process from beginning to end. The presented ECS flowchart is a robust algorithm with proper design and construction, which communicates the steps in the ECS processes very effectively and efficiently.
Program’s Structure Analyses and GUI Construction
The web application and database [21-23] were developed and implemented in a working environment to enable the users to communicate with the database through the fingerprint scanner. Graphical User Interface (GUI) of the web application was built up to facilitate the collection of biometric features of the participants. The GUI consists of username, age, time in, time out, among other numbers of controls (textboxes, combo-boxes, button, etc.). The list of all properties and methods for all controls which allowed the system to communicate with a fingerprint scanner was the Application Programming Interface (API). A set of controls was used to reach the desired purpose, the functionality of the application, including Labels, Text boxes, Combo Boxes, Data Grid, Buttons, Group Boxes, Panels, Tab controls, etc. All of these controls were available in the application and were fitted to the corresponding forms, which were to be filled by the participants.
Windows Forms text boxes are used to get input from the user or to display text. The TextBox control was generally used for editable text, although it can also be made read-only. Text boxes can display multiple lines, wrap text to the size of the control, and add basic formatting. The Windows Forms ComboBox control was used to display data in a drop-down combo box. By default, the ComboBox control appears in two parts: the top part is a text box that allows the user to type a list item. It can be noticed that almost all of the controls are grouped and placed on a special field (platform) and can switch from one group to another by clicking on the responding titles.
ECS Performation Evaluation Process
The employee clocking system requires an employee to establish his or her identity in the system in the first instance. This process is called enrollment; the employee has to present his or her fingers for imaging or scanning. The captured biometrics was processed by the ECS and encryption algorithms. A biometric template was generated as a result of processing, which was stored in a database and associated with identity data of that person. This procedure is part of the enrollment step. The next step is an authentication process where the employee verification of his or her identity, fingerprints are re-scanned, processed, and the new template is compared with the existing one in the database. The matching algorithm returns a match in case of acceptance or nomatch in case of rejection.
Performance Evaluation Matrics of ECS
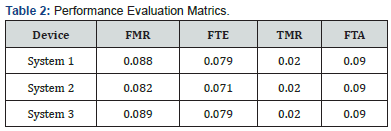
One of the essential factors in the success of a biometric system is its accuracy. The performance is a measure of how well the system can correctly match the biometric information from the same person and avoid falsely checking biometric information from different people. The measurement of biometric accuracy is usually expressed as a percentage or proportion, with the data coming from simulations, laboratory experiments, or field trials. This study used both percentage and proportion in its performance evaluation. There are four principal measures of biometric accuracy:
a) True Acceptance Rate (TAR) / True Match Rate (TMR): This measure represents the degree that the biometric system can match the biometric information from the same person correctly. Developers of biometric systems attempt to maximize this measure.
b) False Acceptance Rate (FAR) / False Match Rate (FMR): This measure represents the degree or frequency where biometric information from one person is falsely reported to match the biometric data from another person. Developers attempt to minimize this measure.
c) True Rejection Rate (TRR) / True Non-Match Rate (TNMR): This measure represents the frequency of cases when biometric information from one person is correctly not matched to any records in a database because that person is not in the database. Developers attempt to maximize this measure.
d) False Rejection Rate (FRR) / False Non-Match Rate (FNMR): This measure represents the frequency of cases when biometric information is not matched against any records in a database when it should have been matched because the person is, in fact, in the database. Developers attempt to minimize this measure.
Other standard biometric accuracy measurements essential for determining the final success of the ECS systems deployed in our work are:
a) Failure-to-enrol rate (FTE): the proportion of the user population for whom the biometric system fails to capture or extract usable information from the biometric sample.
b) Failure-to-acquire rate (FTA): the proportion of verification or identification attempts for which a biometric system is unable to capture a sample or locate an image or signal of sufficient quality.
In addition to these error metrics, other performance metrics are used to ensure the operational use of biometric systems such as
a) average enrollment time
b) average verification time
c) average and maximum template size
d) the maximum amount of memory allocated
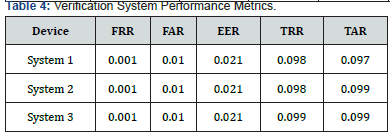
Verification System Performance Metrics
False rejection rate (FRR): the proportion of authentic users that are incorrectly denied. If a verification transaction consists of a single attempt, the false reject rate would be given by:
FRR(τ ) = FTA + FNMR(τ ) * (1− FTA)
False acceptation rate (FAR): the proportion of impostors that are accepted by the biometric system. If a verification transaction consists of a single attempt, the false accept rate would be given by:
FAR(τ ) = FMR(τ ) * (1− FTA)
Equal Error Rate (EER): this error rate corresponds to the point at which the FAR and FRR cross (a compromise between FAR and FRR). It is usually used to evaluate and to compare biometric authentication systems. The more the EER is near to 0%, the better is the performance of the target system.
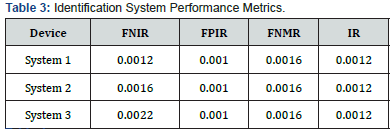
Identification System Performance Metrics
Identification rate (I.R.): The identification rate at rate r is defined as the proportion of identification transactions by users enrolled in the system in which the user’s correct identifier is among those returned.
False-negative identification-error rate (FNIR): The proportion of identification transactions by users enrolled in the system in which the user’s correct identifier is not among those returned. For an identification transaction consisting of one attempt against a database of size N, it is defined as:
FNIR(τ ) = FTA + (1− FTA) * FNMR(τ )
False-positive identification-error rate (FPIR): The proportion of identification transactions by users not enrolled in the system, where an identifier is returned. For an identification transaction consisting of one attempt against a database of size N, it is defined as:
FPIR = (1− FTA) * (1− (1+ FMR)N)
Results and Discussion
The three systems were connected to the same database, which simultaneously checks the fingerprint images with those in the databases. The testing of the system was done three weeks after the employee enrollment was done. The test ensured the all the participants had their biodata tested with the data stored in the database. After four days of testing, we realized that some of the participants had difficulty with the authentication process. To measure this anomaly, we used the performance evaluation matrix to determine the accuracy of the test. True Acceptance Rate, False Acceptance Rate, True Rejection Rate and False Rejection Rate were used to test the results.
Other parameters, such as receiver operating characteristics and Cumulative match characteristic, were represented graphically to determine the performance of the system, which directly ensure that we achieve the objectives of this work.
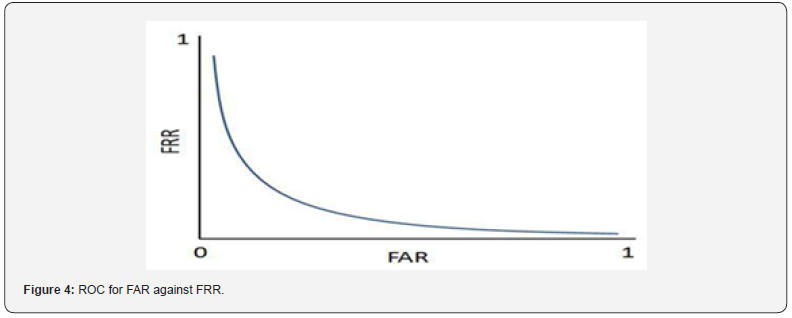
Receiver operating characteristic curve (ROC): the representation of the rate of FMR as well as FAR, thus, accepted impostor attempts on the x-axis against the corresponding rate of FNMR as well as FRR, thus, rejected genuine attempts on the y-axis plotted graphically as a function of the decision threshold. An illustration of a ROC curve has been presented in Figure 4.
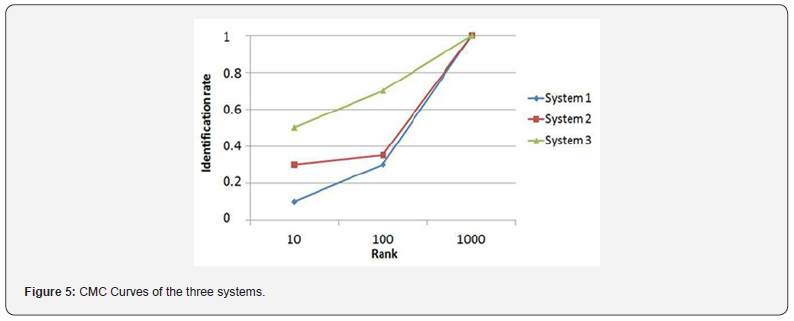
Cumulative match characteristic curve (CMC): this is the graphical representation of results of the identification test, plotting rank values on the x-axis and the probability of correct identification at or below that rank on the y-axis. The CMC curves have been given in Figure 5.
It is interesting to note that the study found a few errors (0.5% to 1.5%) caused by filing fingerprints with the wrong personal information than it found false acceptances by the biometric system. It also found a strong relationship between the quality of the fingerprint images stored at enrollment and the accuracy during verification comparisons.
The best images had TAR=98% at FAR=0.01%, while the worse images had TAR=47% at FAR=0.01%. Finally, this study also showed the value of combining two fingerprints at verification time. When this was done, the accuracy increased to TAR=99.7% when FAR=0.01%, as indicated in Tables 2-4.
Overall, fingerprint matching accuracy suggests that the performance was quite good with high-quality fingerprint images. Caution was appropriate; however, because the results were from a real-world experiment, the actual accuracy much better than the results obtained by [11,13,18].
Conclusion
Introduction
The truancy of employees has affected the productivity of many organizations. This situation has resulted in the loss of revenue, among many other adverse effects. This paper sought to introduce a biometric employee clocking system to help overcome the high level of truancy in workplaces. The results of the experiment we conducted indicate a high accuracy in our system with TAR value of 99.7%. This accuracy rate is much better than the results other researchers obtained. The implication of the good accuracy is that employees will have difficulty to check-in or out for their truant colleagues. The high accuracy results will help improved security of attendance, improved employee performance, ensures fast and easy retrieval of data, easy monitoring of staff, and prevent impersonation in the attendance logs. The automated process, with the aid of fingerprint biometrics, does not give room for impersonation. Once an employee has been enrolled, it cannot be verified by another person.
References
- Abhilash KS (2015)Biometric System - A Review. International Journal of Computer Science and Information Technologies. September.
- Acuity Market Intelligence (2008)Biometrics: high-value workforce management: The critical role of biometric time and attendance to workforce management solutions. White Paper.
- YangW, HuJ, WangS (2017) A Delaunay quadrangle-based fingerprint authentication system with template protection using topology code for local registration and security enhancement. IEEE Trans. Inf. Forensics Security9(7): 1179-1192.
- Tan TN, Lee H (2019) High-secure fingerprint authentication system using ring-LWE cryptography. IEEE Access 7: 23379-23387.
- PangS, JinchunYE, XuH, LiH(2019)U.S. Patent No. 10,496,804. Washington, DC: U.S. Patent and Trademark Office.
- Harikrishnan D, Sunil KN, Joseph S, Nair KK (2019) Towards a fast and secure fingerprint authentication system based on a novel encoding scheme. The International Journal of Electrical Engineering & Education.
- LiuF, ZhaoQ, ZhangD(2020)3D Fingerprint Authentication. In Advanced Fingerprint Recognition: From 3D Shape to Ridge Detail. Springer, Singapore, pp. 33-57.
- Adewole K, Adbulsalam S, Babatunde R, Shittu T,Olotede M(2014)Development of finger biometric attendance system for non-academic staff in a tertiary institution. Computer Engineering and Intelligent Systems Review5(2).
- Akinduyite CO, Adetunmbi AO, Olabode OO, Ibidunmoye EO(2013) Fingerprint-based attendance management system. Journal of Computer Sciences andApplications1(5): 100-105.
- Cupido (2011) The implementation of a time and attendance system at Stellenbosch Municipality - a change management perspective masters project in public administration. University of Stellenbosch.
- Danny T (2019)Biometric System, Biometrics Comparison – biometrics performance metrics can help you select the right biometric solution.
- org. (2017)11 Basic Patterns of Fingerprint.
- Krishna PK, Aithal PS (2017) A Conceptual Study on User Identification and Verification Process Using Face Recognition Techniques. International Journal of Applied Engineering and Management Letters.1(1): 6-17.
- Krishna PK, Aithal PS (2017) Literature Review on Fingerprint Level 1 and Level 2 Features Enhancement to Improve Quality of Image. International Journal of Management, Technology and Social Sciences (IJMTS) 2(2).
- Kuntal B, Samayita B, Kalyani M (2015)Fingerprint Identification, April.
- Karani KP, Aithal PS (2017) A Conceptual Study on Image Enhancement Techniques for Fingerprint Images. International Journal of Applied Engineering and Management Letters (IJAEML) 1(1): 63-72.
- Obansola OY, Makinde OE, Adeshina AH, Adebayo OB (2016) Development of Staff Attendance Management System Using Fingerprint Biometric Identification Technique.
- OmobayoA(2015)Optimization of bimodal biometrics system for access control authentication in Kenya. School of Computing, College of Science. Engineering and technology, University of South Africa.
- Ononiwu GC, OkoraforGN (2012)Radio frequency identification-based attendance system with automatic door unit. Academic Research International2(2).
- Appiah V, Nti IK, Nyarko BO (2017) Investigating Websites and Web Application Vulnerabilities: Web master's Perspective. International Journal of Applied Information Systems (IJAIS) - ISSN: 2249-0868 Foundation of Computer Science FCS, New York, USA, IJAIS Publications12(3).
- Vincent AP, Michael A, Isaac KN, Owusu NB (2018)Survey of Websites and Web Application Security Threats Using Vulnerability Assessment. Journal of Computer Science. Science Publication15(10): 1341-354.
- NyarkoBO, AsanteM,NtiIK(2017)Implementation of Advanced Encryption Standard Algorithm with Key Length of 256 Bits for Preventing Data Loss in an Organization. International Journal of Science and Engineering Applications, IJSER Publications.6(3): 88-94.
- Nyarko BO, Benjamin A, Weyori, Lord AT (2020)Optimized Authentication Model for Online Transaction Payments. Science publications- Journal of Computer Science16(2): 225-234.
- Nyarko BO, Alfred K, Justice A (2017)The Relevance of E-Library Facility to the Delivery of Education at the High School: An Example from Ghana. International Journal of Scientific & Engineering Research. IJSER Publications8(5): 910-918.
- Nyarko BO, AdekoyaAF(2019)Evaluation and analysis of key performance indicators which affect the QoS of mobile call traffic. International Journal of Computer Networks (IJCN)9(1): 14-30.






























