- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Providing Cloud Security by Combining Authentication Methods
Vahid Bahmani1* and Nasab MA 2
1Graduated in Information Technology-Information Security, Iran
2Information Security analyst, Iran
Submission: June 12, 2017; Published: June 29, 2017
*Corresponding author: Vahid Bahmani, Graduated in Information Technology - Information SecurityTehran, Iran, Email: eng.vahid.bahmani@ieee.org
How to cite this article: Vahid B, Nasab M. Providing Cloud Security by Combining Authentication Methods. Mod Appl Bioequiv Availab. 2017; 1(4): 555569.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Abstract
Nowadays, security is frequently referred to as a very important aspect of cloud computing technology. Even though in the shortest form, security provisions can be listed as keeping confidentiality, data integrity, authentication, strict management, fast troubleshooting, consistent access of authorized users to the data, and ensuring the availability of professional ethics, but from the viewpoints of many users and critics, the most sensitive aspect of security is user authentication early when he/she tries to log into the cloud. From this point of view, a user will be able to undertake activities within the scope of cloud data management only once he/she was successfully authenticated, and in cases where an intruder plans to attack via establishment of illegal sessions and unauthorized access to data, he/she will be detected as fast as possible, so that confidentiality and data integrity will be mostly achieved via user authentication by which one can prevent unauthorized sessions or changes in data. In recent years, many researchers have proposed the use of users' biometric information for authentication purposes. In the present paper, different authentication methods using biometric data in cloud computing environment, associated challenges for users and existing threats are investigated together with an expression of available solutions. Furthermore, risk management is utilized to determine asset importance and required level of security for making decisions on the choice of cloud type, encryption techniques, and authentication method. Security constitutes the core of the present paper, and in each section of the paper, the parameter constituting overall scope of the discussion will be the recognition of required level of security and its evaluation at any specific application within cloud environment.
Keywords: Cloud computing; Security; Confidentiality; Data integrity; Authentication; Biometric information; Risk management
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Introduction
Cloud computing is a relatively new topic which needs further attention by experts, so that different classes of community get to know its advantages and incorporate it into their everyday life. Any novel technology should be very lucky to be autonomously welcomed and implemented. In case of technologies like cloud which require to be 100% trusted by the users, security and building trust represent more serious issues. Cloud managers shall undertake provisions upon which users can easily and trustily use the dedicated space to them on the cloud - i.e. there should be the art of providing security in cloud environment. On the other hand, nowadays, computer networks are of considerably large extensions involving all range of jobs including ones in governmental and private sectors. Meanwhile, different conditions between different networks and the importance of resources across that network (e.g. hardware and software resources) have made the resources an essential pillar of the network. The networks have extended beyond the computer and server frameworks and developed into clouds of large capabilities. The clouds encompassed the entire network from equipment to the users planning to use the networks. Now, sensitive issues have raised meanwhile. Among other issues, issues such as security provisioning worth a great deal of attention. There are assets which shall be protected, and since the subject matter of cloud is a relatively new yet popular topic, a reliable solution for providing it with security is yet to be proposed, bringing the cloud security at the center of attention by both researchers and intruders. Clouds were first designed and implemented with different specific functions, but those are further developing on a daily basis. Now, considering the importance of clouds and resources within them, one shall undertake appropriate measures to provide clouds with security in different aspects. Cloud computing was developed to provide users with easy access, lower cost, faster computations, integrate services, etc. However, within the scope of the present paper, the main objective of this service is to provide users with easy and fast on-demand access to their own storage and computing space on the cloud, so that infrastructural limitations remain completely clear for the user while the user is able, based on a predefined level of freedom and access, to submit required requests and undertake required processes; and on the other hand, no other user can access, using his/her own identity, to access another user's private space, while authored accesses may not be associated with any sense of limitation, i.e. a secure working environment and a large deal of respect under the effect of cloud computing technology. For this purpose, we will have our focus on the point that, in each cloud model (e.g. private, public, or combined) it is possible to choose security level and encryption method and user authentication based on capabilities and characteristics of the respective cloud. As a result, one should begin with analyzing data type and its requirements using risk management.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Definition of Cloud Computing
National Institute of Technology and Standards have defined cloud computing as follows: cloud computing is a model for providing easy access, upon user request and via network, to a set of changeable and configurable computing resources (networks, servers, storage space, applications, services). The access should be established/released as fast as possible at the lowest possible need for resource management/direct intervention by service provider [1]. Cloud computing is a technology wherein Internet and Central Service Provider are used to maintain data and application, so that consumers can utilize their applications and data without being required to have the applications installed or even purchased. This technology provides a basis upon which, instead of personal storages, users can use the possibility to access their applications and data wherever they have access to Internet, and to easily backup their data with no need to knowledge of usage management and backup creation. For this purpose, the common approach is to sign a contract between cloud maintenance companies and subscribers. Service level agreement (SLA) is a sort of contract which ensures a certain level of service quality to be provided by the service provider company to the served company or user. Service providers provide a variety of services with different models at different prices upon agreed services and qualities; this makes it complicated to select a service and this represents the point at which security problems begin. Many service receivers practice cloud selection based upon the mentioned criteria only without adequate knowledge of security requirements of the specific business and assets.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
General Challenges of Cloud Computing
Since users recognize a general cloud as being at high risk, cloud service providers should provide users with such provisions as SLA to ensure the users in terms of security and privacy control on their data and application. Prior to that, however, the point on which authors of the present paper place an emphasis is the codification of standards in accordance with national regulations of different countries and local users' needs, and at a higher level, codification of similar international standards in general, where businesses classification and required level of security for each class is taken into account. Accordingly, duties of service provider and service receiver will be specified on a general scale and then, using risk management, service receivers (especially owners of businesses directly related to information) begin with evaluating security value of their assets and information, and depending on the calculated quantities of risk factor, they go for selecting appropriate type of cloud and user authentication algorithm. Finally, based upon the selection, an agreement will be signed.
SLA is a legal agreement between cloud service provider and receiver which not only addresses appropriate performance of user authentication service which affects the performance of any other service, but also present clear-cut duties and rights of either parties.
SLA is composed of the following sections:
- Customer needs identification and definition
- Simplification of complicated problems
- Reduction of areas of conflicts among user
- Encouragement to negotiate on conflicts
- Clear-cutting and elimination of unrealistic expectations
- Providing a framework for easier understanding of operations in cloud computing
In many cases, of course, cloud computing service providers outsource required resources, and even under some conditions, storage equipment are outsourced from external organizations. Many of these outsourcing practices will be controlled against SLA for covering security aspects including data integrity and reliability.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Comparison and Analysis of Active Authentication Methods
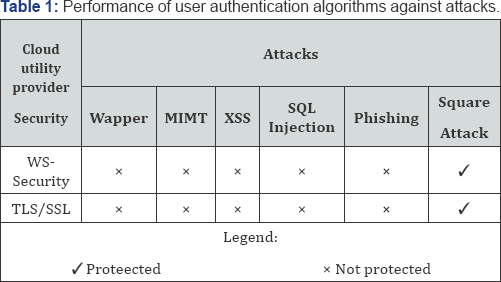
By considering security designs in cloud computing such as Web Services Security (WS-Security) and Transport Layer Security (TLS)/ Secure Sockets Layer (SSL) against wrapper attack, Man-in-the-Middle (MITM) attack, and Cross Site Scripting (XSS) attack, vulnerability of these designs against these attacks is presented in the following (Table 1)
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Authentication Methods, Tricks for Fraud Prevention
Biometric characteristics represent one of the solutions for user identification, using which appearance features of individuals serves as unique personality of the individuals. This solution involves collecting digital data from user's body nature. In this method, input data is submitted to the system through a system which is to import required parameters for user authentication. After that, the submitted data is analyzed using a signal processing algorithm. Once data was transferred to the central system, the parameters are checked by the system, with this dataset serving as user's bio-signature. Continuing with the process, the algorithm searches its database for an individual with imported parameters. Indeed, imported data is compared against the data in database and in case a match was found, the user will be provided with access to his/her private space [2,3]. A wide spectrum of features in human body can be used for this purpose.
The reason for using this authentication method is the uniqueness of identification patterns such as fingerprint, iris of the eyes, voice spectra characteristics, facial features, gait patterns, typing patterns, DNA configuration, etc. for any single person, so that one can invest on uniqueness of each and any piece of such data [4].
Since each of the above-mentioned methods for personal identification is associated with certain weaknesses, abuses are possible in case of attacks to either method. However, in cases where we are working with high-risk data, it is better to combine the authentication method with a secondary method such as the use of DSA algorithm to further enhance security level. Even though each of these technologies are developed upon principles to prevent fraud, but regarding the fingerprint for instance, if an intruder captures an authorized user's fingerprint from a bottle of drink, he/she may successfully manage to attack the system. Or in other cases, it is possible for the system to be deceived when trying to identify iris. Regarding voice detection- based identification, technological advancements have given rise to synthesizer tools which can convert one person's voice frequency to another's [5]. In order to address this challenge, combined biological identification methods with digital signature algorithms of adequately long keys and encryption methods are proposed and investigated by the present paper. If user's biological data including heart beat or blood pressure are stored in the corresponding database on a regular basis, one can use this information to generate encryption keys.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Modern Biometric Authentication
In order to mitigate the mentioned challenges and provide the possibility to use biometric information for authentication purposes, researchers have proposed various methods such as the use of modern biometric detections to access sensitive data based on skin resistance which is one of the important and effective factors in neural processing for adjusting body mechanism. The question, however, is that can one achieve a reliable user authentication method based on processed electro dermal responses acquired using sensors? And is such an approach applicable in cloud processing? [1]
The proposers of this design have recognized the use of vital signals asabasis for thisnovel approach tobiometricidentification. Cognitive biometrics refers to the transmission of signals such as electroencephalography (EEG), electrocardiography (ECG), and electro dialysis reversal (EDR) signals as input to an authentication system which can use the signals separately or in a multi-step biometric user authentication process. The data generated by these signals is acquired using the technology of implanting electrodes at appropriate positions on human body (head and arms); the signals are then transmitted to the system. Normally, required data can be received from the body and sent to the authentication system within 1 min. The data is then immediately analyzed. It should be noted that, the implantation and residence of these electrodes within human bodies are done painlessly, with the carrier of the electrodes not disturbed at all. Anyway, the electrodes always need some gel to be used as a supply of required wetness, and one can use EEG electrodes as a workaround for this issue. The EEG electrodes do not require any conductive gel as those can generate respective signals and transmit them accordingly by being attached to human body in dry state. The electrodes can be permanently fixed to body, and since those use internal and behavioral characteristics of the carrier simultaneously, are able to prevent attacks from multiple angles. On the other hand, sometimes different systems require different documents and IDs to authenticate a user In this case, to be authenticated, the user should keep with him/herself other required documents than the implanted sensors. For such cases, the present paper proposes [3,1] an integrated authentication mechanism using zero-knowledge protocol (ZKP) and Rijndael algorithm in advanced encryption standard (AES).

Zero-Knowledge Proof (ZKP) is a powerful encryption protocol which can be used in many encryption, authentication operation, and key exchange applications. ZKP is a unique approach which claims keeping confidentiality of data without the need for disclosing minimum amount of information. As claimed by ZKP, using ZKP, a user can have him/her authenticated without the need for disclosing any information on the key with the authenticator (Figure 1).
Using a symmetric algorithm like AES, Rijndael algorithm can save significant deals of time and computation cost while increasing the level of security. Good computational efficiency of this design is a result of using a symmetric encryption system and fast pace of calculations.
The generated key in this algorithm is 128 bits in length, indicating considerably smaller length for this key compared to those of asymmetric algorithms. This is while the key still provides an acceptable level of security. In addition, due to the use of a simple algorithm for generating this key, there is no need for purchasing advanced computer systems to undertake respective encryption computations. Rijndael algorithm is a key-generating algorithm using symmetric encryption which ends up with an iterative password block, i.e. initial input block together with encryption key are multiple-times subjected to the algorithm in the evolution cycle before producing the final output [5]. Furthermore, length of the key varies depending on the desired level of security. Therefore, once finished with undertaking risk management operations on organizational assets, one can use keys of 128, 192, or 256 bits in length depending on the desired level of security. This algorithm is in accordance with the main idea of the present paper and can provide various levels of security by generating keys of different lengths.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Modern Identification and Authentication on Cloud
Application programming interface (API) authentication method uses an identification mechanism. Used in this method are electro dermal sensors which are attached to the body using some probes, and acquire biometric data before submitting them to the authentication system. Thus, once a user requests for connection to get access to cloud services, the authentication system uses electro dermal sensor responses to acquire required data and user information. Electrodermal responses provide the system with such information as user's mental and behavioral conditions. Accordingly, two things are checked in fact: 1) dose the person provides the right identity and is he/she an authorized person? And 2) is he/she of proper mental conditions to be provided with access to data or is he/she willing to maliciously damage data or maybe unwontedly forced to connect the system? [1]
In order to prevent user's biometric authentication information from being stolen, these data shall be encrypted regardless of the mode and equipment selected to handle these data. On the other end, user identification and authentication system decrypts the encrypted data by the user's key and checks for data integrity and correctness. Also in this method, one can select different types of encryption and different lengths of encryption key depending on the sensitivity of data [1].
As was mentioned, in the hierarchy followed in cloud authentication system, not only user's identity is checked, but also his/her intention for logging into system and access data is also analyzed. This is done by considering prior performance and records of the user together with received biometric information from him/her during previous sessions as compared to current information in terms of resources used and the way these resources are used. In other words, each time a user requests for logging into the cloud, the cloud authentication system reviews previous orders by and actions and received biometric information of the user in previous sessions. Then, if it was clear for the system that the user has not raised any trouble for the cloud system and his/her mental state is not problematic (as compared to previous sessions), the system authenticates the user for log in. On the other hand, micro-sensors implanted into skin and different muscles may exhibit different conductance values, but the system can operate immediately if it is well calibrated in advance, ending up with no problem. Skin conductance response (SCR) is very sensitive to such feelings as fear, rage, and sexual senses [2], so that it can precisely distinguish these feelings even though these are very similar to one another. These sensors are also used in lie detector polygraphs.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Criticism, Investigation and Solution of Novel Biometric Identification
In addition to such problems as failure to encrypt XML files and failure to use digital certificates in this method which tend to end up with MITM attacks and information theft, this protocol follows a strict approach which makes it a not- recommended alternative for the data requiring normal security levels. However, one should remember that we should always establish a balance between accessibility and security level. In the mentioned method (i.e. checking physical and mental states of individuals for authentication purposes), even though the challenge of biometric information fraud is mostly mitigated, but since natural mental states cannot be changed, it is always possible for users to have their access to the cloud denied, which is in contradictory with one of the fundamental objectives of cloud computing: ease of access.
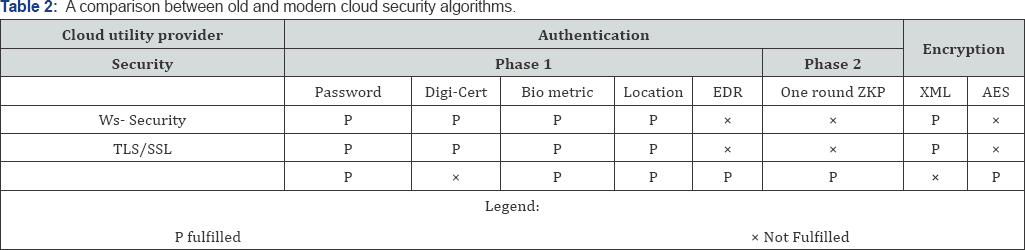
As such, when it comes to typical data, the use of biometric method and encryption of biometric data prior to having them transmitted is recommended as the optimum solution. Accordingly, in order to enhance efficiency and reduce computational cost, one can use symmetric encryption methods and use general key-generating algorithms only when transmitting the secret key. Moreover, respecting related points regarding MITM attacks, Diffie-Hellman key exchange protocol can be used to generate shared key, practically eliminating the need for sending a shared key. In this case, depending on the desired level of security and computational power of the used , Computers one can use Al-Jamal signature or generic key-based methods for encrypting the information sent from the requester (Table 2).
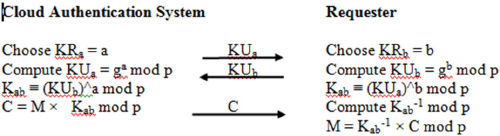
In Diffie-Hellman key exchange protocol, a value is chosen by either of parties as well as the identification system before parties of the protocol uses a group generator to produce a shared key as follows:
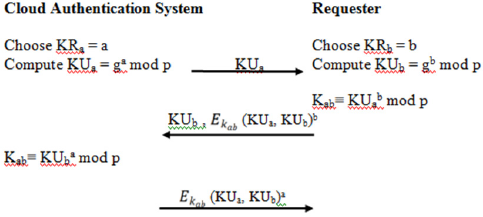
In this method, in spite of failure to use a trusted third party, MITM is not possible as well. For this reason, the assumption of taking Z*p as the far group and g as the generator of this group is valid. This protocol is implemented following steps below: Requester selects a large random number, a. this number can be chosen by involving such numbers as heart beat rate or Allice blood pressure, in case where these values have been well recorded on a regular basis. In this way, this private key will be provided with some sort of time stamp. Allice uses the group generator to calculate KUa or its own generic key, and then sent the obtained value to the cloud authentication system
The authentication system also choses a large random number, b, and applies the group generator to calculate the value of KHb and then Kab. The system then signs the values of KUa and KUb using its private key, encrypts the result using Kab and send the results together with KUb to the requester. The requester then begins with calculating Kab. Then it goes for decrypting the received encrypted message followed by checking the contained information. If the information was approved, it calculates KUa and KUb to the power of its private key, encrypts the result using Kab key and send it back to the authentication system. The authentication system decrypts the received message and verifies the signature similar to what was done by the requestor.
If the shared key is verified by both parties, the two parties can communicate securely. Now, the requester can use the common secret key to encrypt his/her own biological information and other messages/requests before sending them to the authentication system on-demand. In this way, authentication will be possible through a multi-layer and fully secure structure, making the MITM attack impossible to practice. As was noticed, Al-Jamal algorithm can be used for encryption purposes to send information in the second layer. In this method, Diffie-Hellman key exchange protocol is used to generate shared key. The security of this algorithm is based on the difficulty of discrete logarithmic problems which results in an acceptable level of security. However, one cannot expect good performance considering the slow execution of this algorithm In this encryption algorithm, each user uses three parameters to conclude the algorithm. Taking Z*p as the far group and g as the generator of this group, the protocol is implemented as follows:
The above algorithm is not recommended for cases where we are left with machines of low computation capabilities or large volumes of data at low security levels.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
Conclusion
As of now, most of authentication systems are based on various encryption methods and digital signatures, or they work via biometric indicators such as fingerprints, voice match processing, or still rely on traditional methods such as passwords for authentication purposes. As it was observed, old biometric- based solutions have been associated with possible frauds and successful attacks, while modern biometric approaches based on electro dermal information of patient are also not applicable in all instances due to the strict approach they tended to follow. On the other hand, clouds host a wide spectrum of businesses extended from small companies to giant industries, which are different in terms of required equipment, information, and some times the level of knowledge and awareness of their users. As was also mentioned, in order to compensate for inadequate awareness among the users, one needs standards and documentations based on international and local regulations. In the next step, these standards can trigger risk management operations in sensitive cases, finally providing a basis for appropriate choice of cloud type. It was recommended that, for different types of cloud, considering the diversity of information and security requirements, risk management results be used to determine required level of security for the authentication process, based on which one can select appropriate security protocols for the user.
Finally, it was observed that simultaneous use of biometric information along with digital signatures or biometric information along with a mix of symmetric and asymmetric encryption methods for sensitive data can effectively contribute to security preservation while not reducing the level of accessibility of private information by authorized users.
- Research Article
- Abstract
- Introduction
- Definition of Cloud Computing
- General Challenges of Cloud Computing
- Comparison and Analysis of Active Authentication Me thods
- Authentication Methods, Tricks for Fraud Preventio
- Modern Biometric Authentication
- Modern Identification and Authentication on Cloud
- Criticism, Investigation and Solution of Novel Biome tric Identification
- Conclusion
- References
References
- Bhavani JL (2012) Construction and Maintenance of a Secured Dynamic Cluster- Based Wireless Sensor. MJIIT-JUC Joint Symposium, Kuala Lumpur, Malaysia
- Yasuaki Ohtaki AS (2009) Integration of Psycho- physiological and behavioural indicators with Ambulatory Tracking for Momentum Indoor Activity Assessment. ICROS-SICE International Joint.
- Bhavani JL (2008) A Secured Dynamic Cluster-Based Wireless Sensor Network Fourth International Conference on Computational Intelligence, Communication Systems and Networks. (CICSyN 208), IEEE Thailand Section, Phuket, Thailand.
- Wu Z (2008) Biometrics Authentication System on Open Network and Security Analysis. International Symposium on Electronic Commerce and Security, p. 1.
- Webb WK (2004) Biometric Security Solution. In Biometrics for Network Security. IEEE computer society 1(2): 376.